Note: This project/blog post was originally started about a year ago, and is written from that perspective.
One of my old roommates decided to give me his hold mechanical keyboard several months ago, a Razer Blackwidow Ultimate Stealth 2016, due to some of the switches no longer working. As I had also been working on some reverse engineering efforts for my Drevo Gramr, I decided to try seeing if I could get QMK working on the board, or at least see how far I could get. Having the ability to reprogram it and use it without Razer’s software would be really cool, and potentially beneficial to a lot of people.
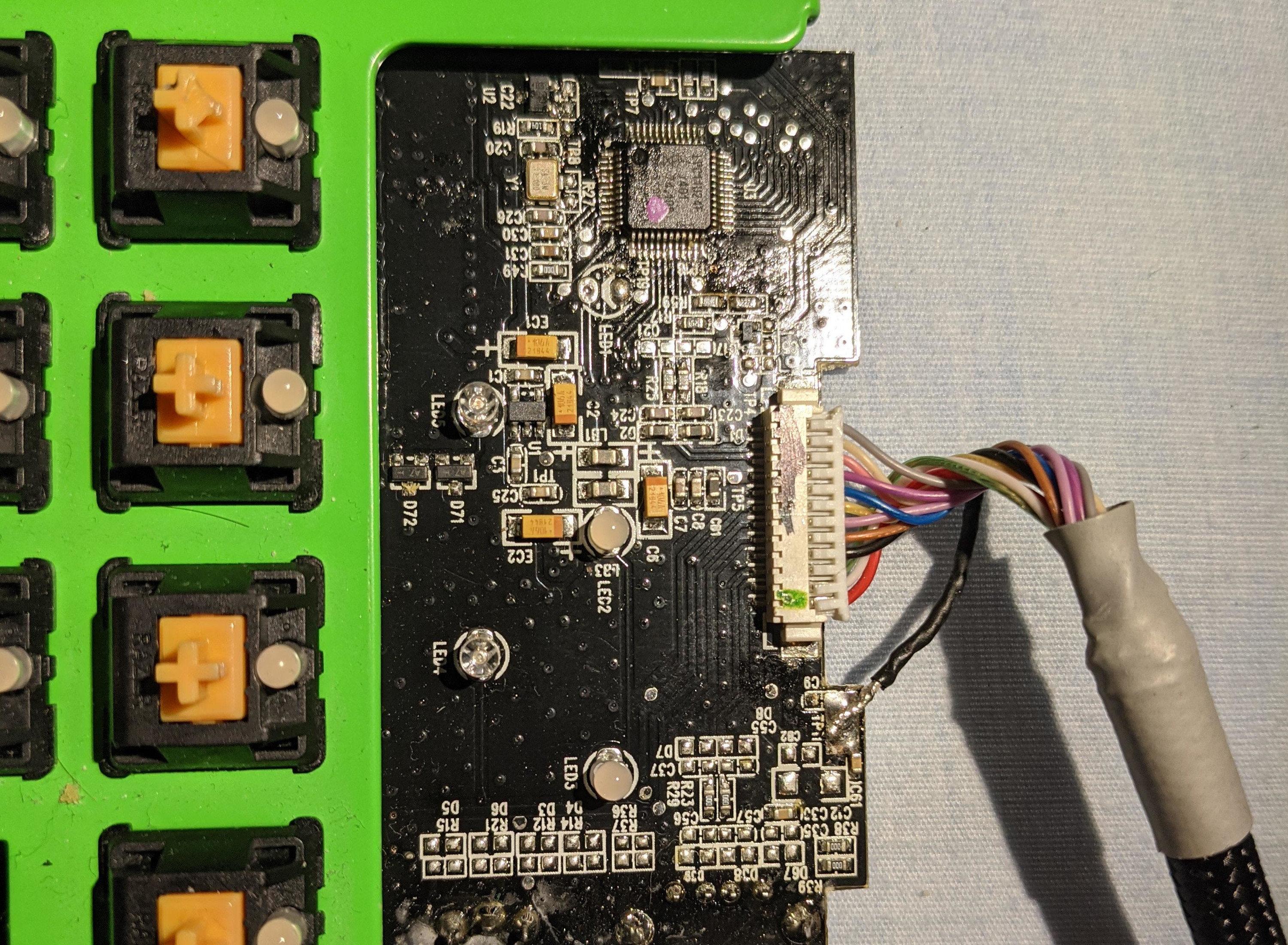
After disassembly and cleaning, I found it had an LPC11U24F microcontroller, which has a lot more documentation for it compared to the off-brand chip found in the Gramr. Surprisingly, during my research I found I wasn’t the only one trying to get QMK working on this microcontroller. I came across this issue on the QMK firmware GitHub repository, and decided to try working with them to see what we could accomplish.
I downloaded the QMK source code and began working on compiling a very basic prototype for flashing to the board; none of the key maps or anything would be correct until I reverse engineered the pin layout, but at least for now it would allow it to show up as a USB device, and work could continue from there.
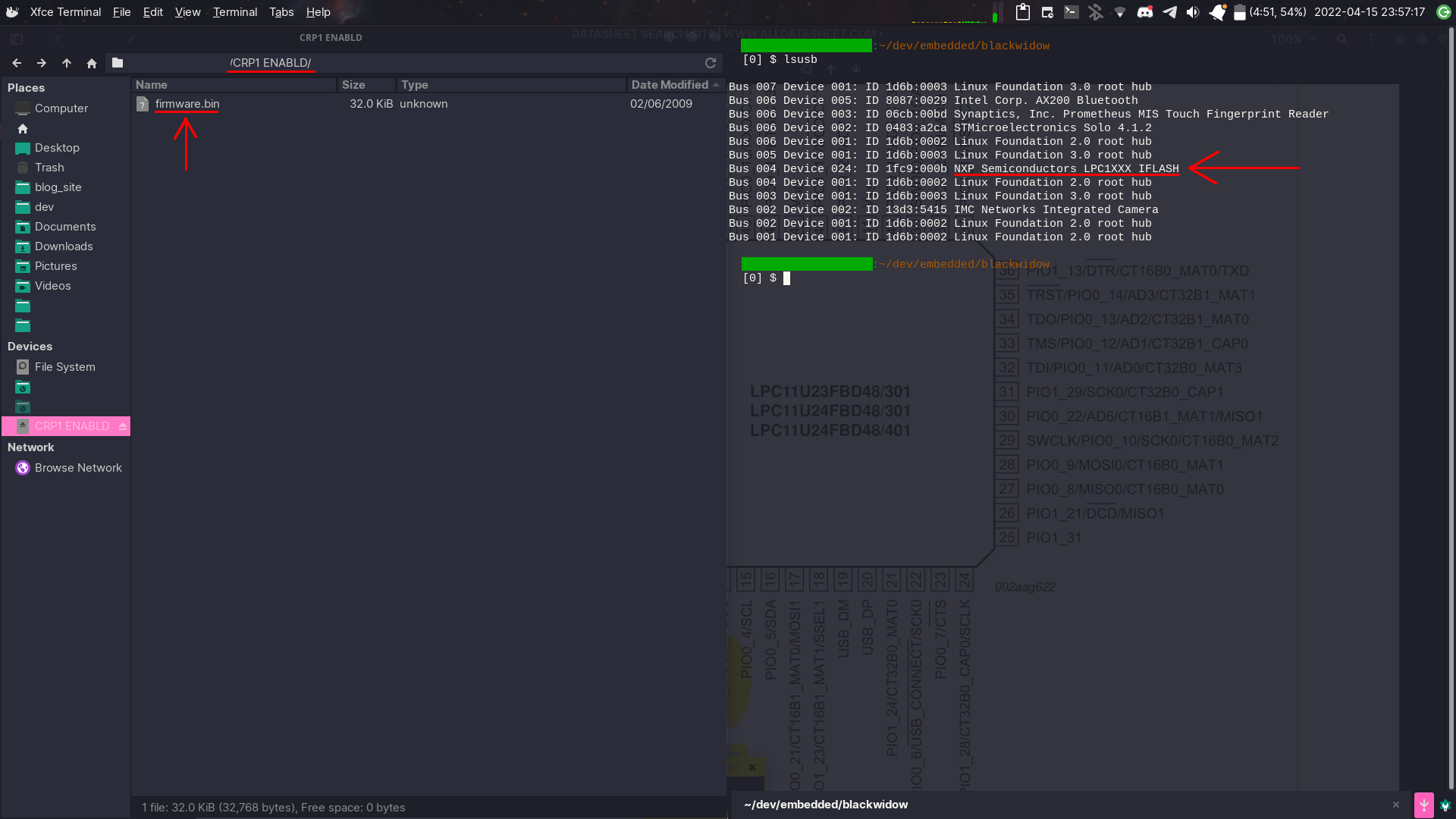
I found that the microcontroller has a USB Mass storage mode on-board for updating the firmware, and so after some trial and error soldering some wires to the board, I was able to make it show up and decided to make a copy of (what I thought) was the original firmware off the board. After copying over the test firmware, I got it to show up as a USB device under a different name! Unfortunately this was when I realized that I couldn’t reflash the original firmware. Little did I know that the microcontroller actually had a protected mode enabled, meaning I was simply copying a file of all zeroes, so I was stuck with a broken board unless I got QMK working. Reverse engineering tip for the future: make sure your backups are actually backups!
I tried running the firmware update utility from Razer to get the original firmware, but I believe it communicates with the software on the chip to actually update it, so it didn’t show up nor work. I tried looking through the files of the updater as well but couldn’t find any firmware files.
That is where I am now, unfortunately. I am still in the progress of figuring out the pinout, which is a very time consuming task, as well as trying to see if I can get a copy of the original firmware. I did buy a second one on eBay for cheap cause it was missing one of the keys, hoping I could run the firmware updater and it would leave a copy of it behind, but unfortunately things in life have distracted me and I haven’t come back to this yet. Hopefully I will soon though because I love reverse engineering stuff like this.
Pictures of the board are available here, for those interested. The source code for the start of the port is also available here. I hope to create an update post sometime soon with more progress, but we’ll see where life takes me.